New SailPoint ISC Capabilities: Entitlement & Role Updates
Date Posted:
Category:
Security
Author:
Nachimuthu

New SailPoint ISC Capabilities: Entitlement & Role Updates
Date Posted:
Category:
Security
Author:
Nachimuthu

New SailPoint ISC Capabilities: Entitlement & Role Updates
Date Posted:
Category:
Security
Author:
Nachimuthu
New Capabilities in SailPoint ISC
As organizations grow, maintaining a right identity model often leads to "identity debt"—outdated roles and broken entitlement links that create security gaps. To address this, SailPoint has introduced two critical updates to Identity Security Cloud (ISC) designed to ensure continuity and correct automation.
Entitlement Rename & Move addresses a long-standing issue by keeping a clear and consistent access trail, ensuring that permissions stay accurate even when objects in Active Directory or Azure are changed. The other one, Role Change Propagation, reduces the gap between policy and practice by making sure that any update to a role is instantly applied to all linked identities. This helps reduce the need for manual adjustments and strengthens the organization's overall security.
Entitlement Rename and Move
Existing Behavior:
When an entitlement's Distinguished Name (DN) was modified in an Active Directory or Azure source, ISC couldn't link the renamed entitlement to its matching entitlement in ISC.
Result:
Entitlement references within roles and access profiles became invalid, and there was a loss of entitlement owner, display name, and access request information.
New Change:
ISC can now smoothly handle entitlements that have been renamed or moved within MS Active Directory or Azure sources.
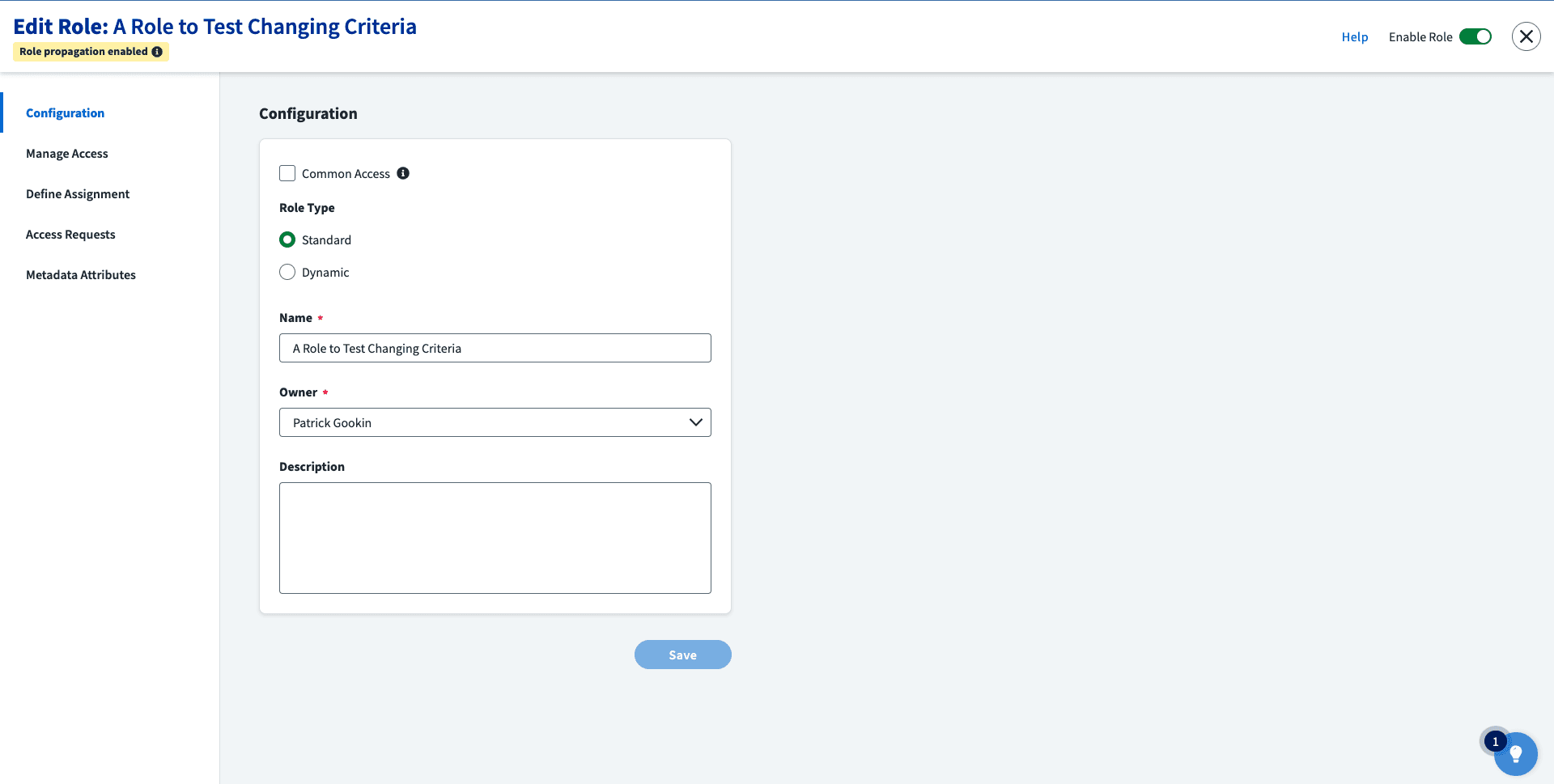
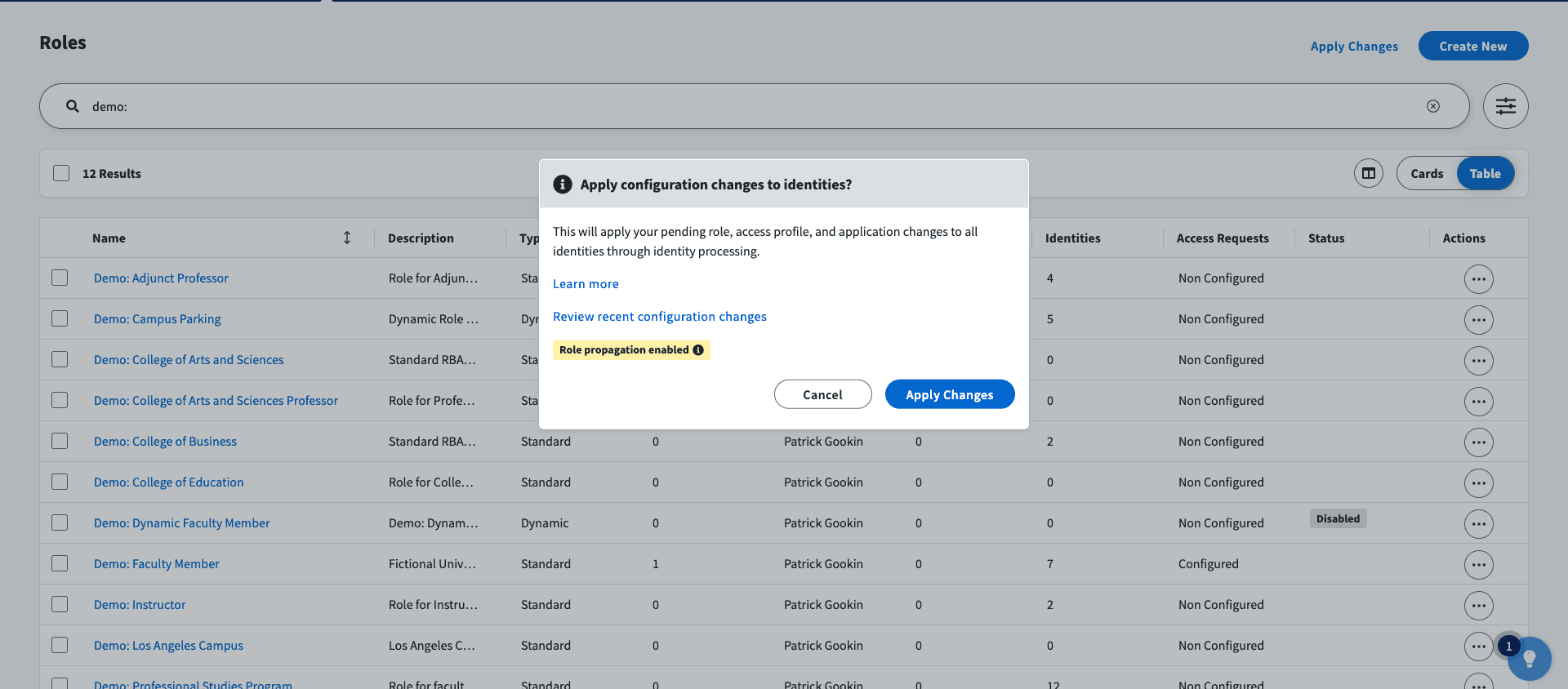
Role change Propagation
Existing Behavior:
In the ISC current setup, removing access from a Role does not automatically remove those same from the users to whom that Role is assigned. This can result in access creep, increasing the security risks.
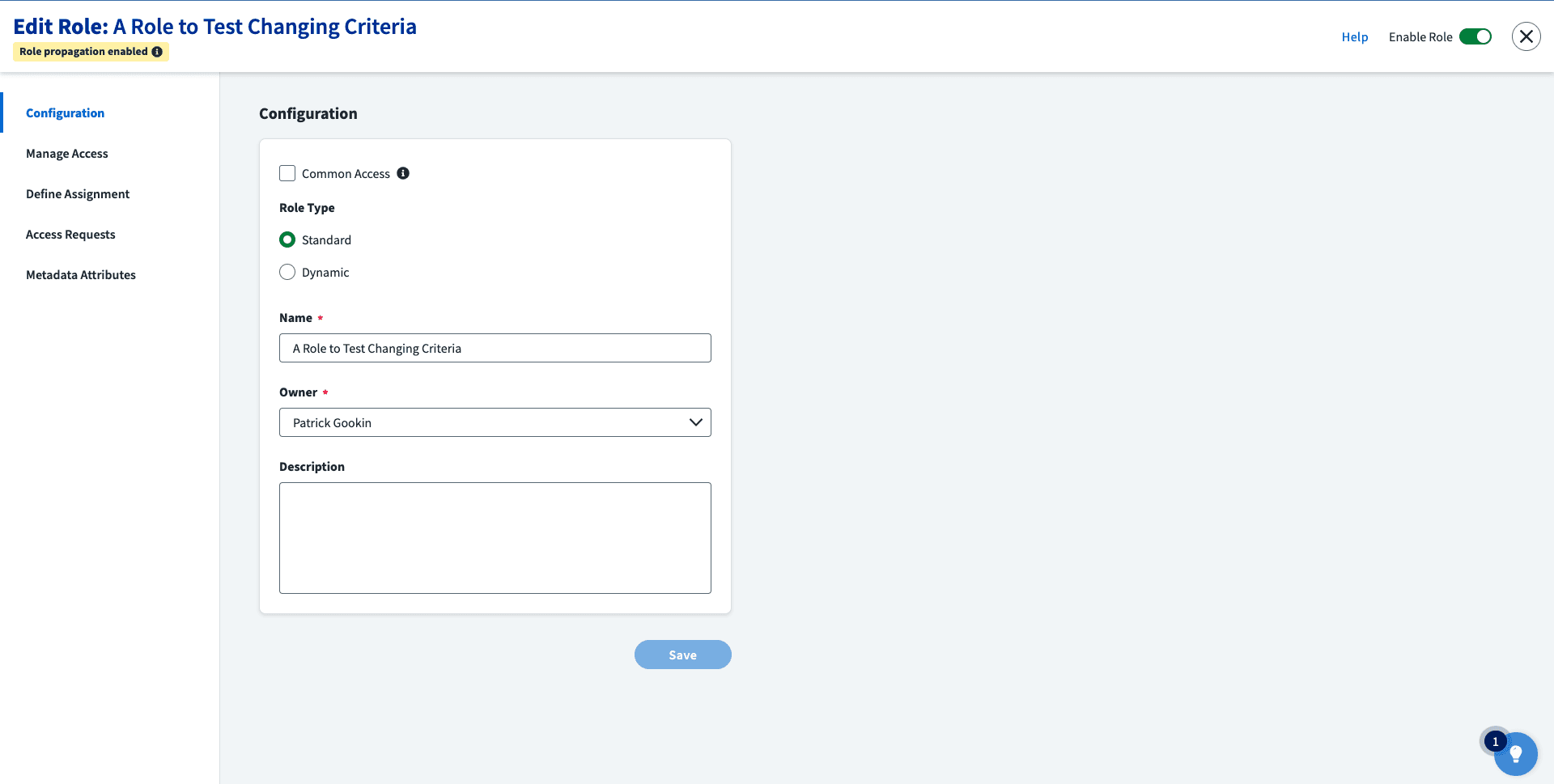
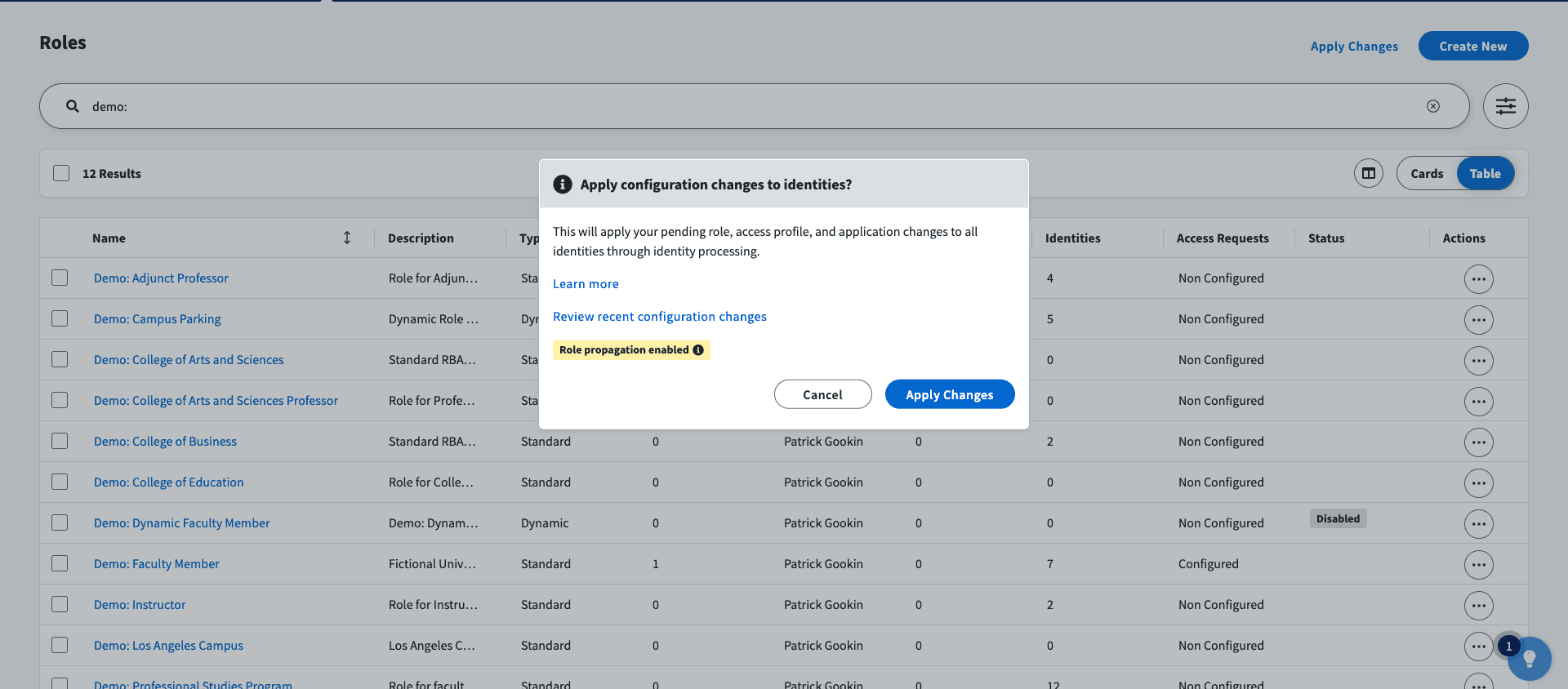
Role Change Propagation allows to configure ISC so that when access is/are removed from a Role, the same is/are removed from users who have the Role assigned to them.
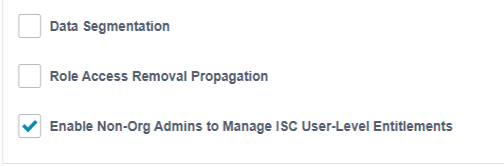
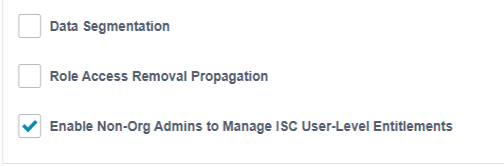
Note: This feature is optional. There's a Global Setting that lets you turn it on or off.
Role change Propagation Scenarios
If the following access rights are removed from a Role's definition, the corresponding access assignments will also be removed from the users who have that Role assigned:
• Removal of an Entitlement from a Role
• Removal of an Access Profile from a Role
• Removal of an entitlement from an Access Profile included in a Role
By eliminating manual cleanup and preventing broken access items, these features help to prevent accidental over-provisioning that often leads to security vulnerabilities.
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Category:
Security
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Category:
Category:
Security
Security
Get your
Tailored Quote for your
Organisation
Get your
Tailored Quote for your
Organisation
New Capabilities in SailPoint ISC
As organizations grow, maintaining a right identity model often leads to "identity debt"—outdated roles and broken entitlement links that create security gaps. To address this, SailPoint has introduced two critical updates to Identity Security Cloud (ISC) designed to ensure continuity and correct automation.
Entitlement Rename & Move addresses a long-standing issue by keeping a clear and consistent access trail, ensuring that permissions stay accurate even when objects in Active Directory or Azure are changed. The other one, Role Change Propagation, reduces the gap between policy and practice by making sure that any update to a role is instantly applied to all linked identities. This helps reduce the need for manual adjustments and strengthens the organization's overall security.
Entitlement Rename and Move
Existing Behavior:
When an entitlement's Distinguished Name (DN) was modified in an Active Directory or Azure source, ISC couldn't link the renamed entitlement to its matching entitlement in ISC.
Result:
Entitlement references within roles and access profiles became invalid, and there was a loss of entitlement owner, display name, and access request information.
New Change:
ISC can now smoothly handle entitlements that have been renamed or moved within MS Active Directory or Azure sources.
Role change Propagation
Existing Behavior:
In the ISC current setup, removing access from a Role does not automatically remove those same from the users to whom that Role is assigned. This can result in access creep, increasing the security risks.
Role Change Propagation allows to configure ISC so that when access is/are removed from a Role, the same is/are removed from users who have the Role assigned to them.
Note: This feature is optional. There's a Global Setting that lets you turn it on or off.
Role change Propagation Scenarios
If the following access rights are removed from a Role's definition, the corresponding access assignments will also be removed from the users who have that Role assigned:
• Removal of an Entitlement from a Role
• Removal of an Access Profile from a Role
• Removal of an entitlement from an Access Profile included in a Role
By eliminating manual cleanup and preventing broken access items, these features help to prevent accidental over-provisioning that often leads to security vulnerabilities.