SailPoint Data Access Security Guide: Roles & Setup
Date Posted:
Category:
Security
Author:
Dhanasekar

SailPoint Data Access Security Guide: Roles & Setup
Date Posted:
Category:
Security
Author:
Dhanasekar

SailPoint Data Access Security Guide: Roles & Setup
Date Posted:
Category:
Security
Author:
Dhanasekar
Overview of Data Access Security
SailPoint Data Access Security empowers associations to discover, govern, and secure critical unshaped data and cover it from critical security pitfalls. Designed as an intertwined SaaS result with Identity Security Cloud.
Prerequisites
1. Produce Virtual Appliance
This configuration is done in Identity Security Cloud.
2. Connect to Identity Security Cloud
Identity Security Cloud that directors can grant to druggies about DAS places.
3. Produce original Sources
Application for identity information need to be created in Security Cloud
4. Produce Identity Collector
This configuration is done in DAS
5. Add an operation
This configuration is done in DAS
Supported Languages
Data Access Security supports further than 10 languages, with American English being the dereliction
• Chinese (Simplified)
• Chinese (Traditional)
• Dutch
• English
• French (France)
• German
• Italian
• Japanese
• Portuguese (Brazil)
• Spanish
• Swedish
User Level
1. Auditor
The rights include
• Monitoring and managing all reports.
• Monitoring and running the forensic.
• Deleting report templates.
2. Data Owner
• Monitoring and managing access information for business files in their compass.
3. Compliance Manager
• Configuring data, rules, and policy objects.
• Viewing data forensics.
• Monitoring and running most reports.
This part doesn't have the Report Template Administrator right.
4.Administrator
• View the admin dashboard and statistics.
• Monitoring and manager access information for all business files.
• Configure settings for DAS.
• Access rights granted to anyone with director capability.
• Report Templates Administrator right.
Connect to Identity Security Cloud
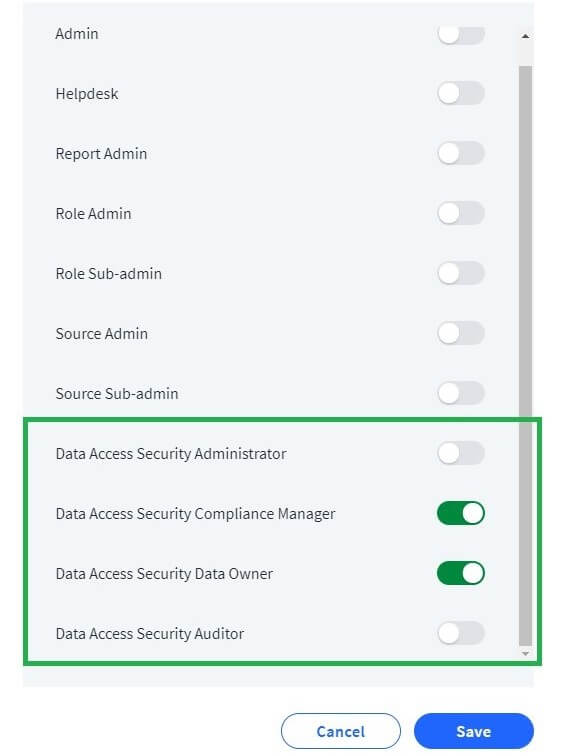
User situations in Identity Security Cloud define authorization sets assigned by administrators. Only ISC Admins can grant or remove them. Users may have multiple situations, combining all associated warrants.
Steps
1. Subscribe into your association (ISC).
2. Navigate to Admin > Identities > Identity List
3. For any being identity elect the perpendicular menu button.
4. Select the Set User Level option.
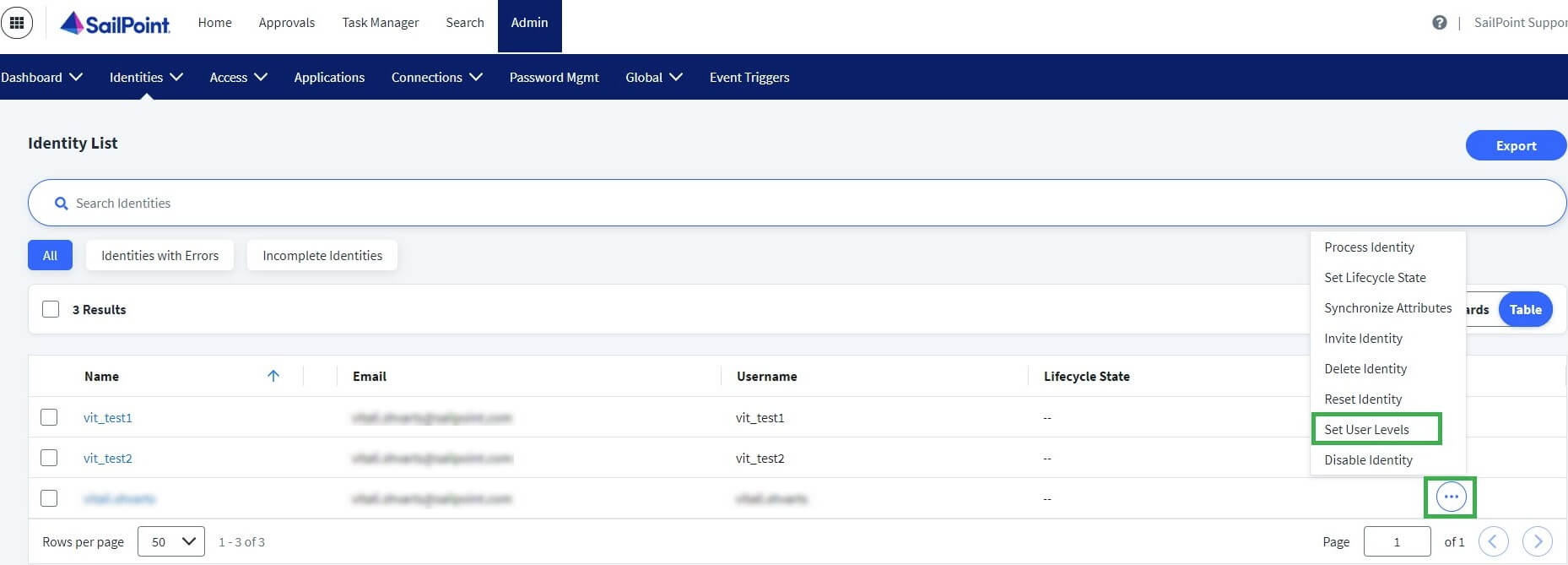
Scroll down and select the applicable Data Access Security parts
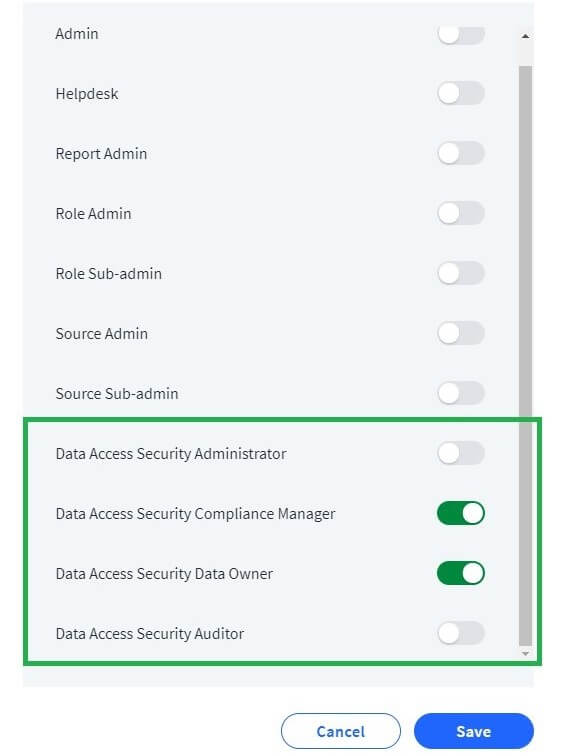
Select Save.
Data Access Security Virtual Appliance Cluster Creation
Data Access Security uses virtual appliances to connect to on- demesne or pall operations and sources. Specialized virtual appliances are also needed to perform Data Bracket across all operation types.
Application Infrastructure | Crawl | Permission Collection | Data Classification | Activity Monitoring |
|---|---|---|---|---|
Cloud (O365, AWS S3, etc.) | N/A | N/A | Data Access Security - Data Classification Collector | N/A |
On Premise (Windows Server, Netapp, etc.) | Data Access Security - Resource Collector | Data Access Security - Permission Collector | Data Access Security - Data Classification Collector | Data Access Security – Activity Monitor |
Connectors
O365 train Storage Microsoft OneDrive for Business
Microsoft SharePoint Online (Office 365)
Microsoft Exchange Online (Office 365)
Pall train Storage Box
Dropbox
Google Drive
NetApp
Powerscale
Unity SMB
Conclusion
SailPoint Data Access Security helps identify and protect sensitive unstructured data. It connects data access with user identities through Identity Security Cloud. Virtual Appliances enable discovery, permissions, classification, and monitoring. Overall, DAS reduces data risk and improves security and compliance.
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Category:
Security
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Category:
Category:
Security
Security
Get your
Tailored Quote for your
Organisation
Get your
Tailored Quote for your
Organisation
Overview of Data Access Security
SailPoint Data Access Security empowers associations to discover, govern, and secure critical unshaped data and cover it from critical security pitfalls. Designed as an intertwined SaaS result with Identity Security Cloud.
Prerequisites
1. Produce Virtual Appliance
This configuration is done in Identity Security Cloud.
2. Connect to Identity Security Cloud
Identity Security Cloud that directors can grant to druggies about DAS places.
3. Produce original Sources
Application for identity information need to be created in Security Cloud
4. Produce Identity Collector
This configuration is done in DAS
5. Add an operation
This configuration is done in DAS
Supported Languages
Data Access Security supports further than 10 languages, with American English being the dereliction
• Chinese (Simplified)
• Chinese (Traditional)
• Dutch
• English
• French (France)
• German
• Italian
• Japanese
• Portuguese (Brazil)
• Spanish
• Swedish
User Level
1. Auditor
The rights include
• Monitoring and managing all reports.
• Monitoring and running the forensic.
• Deleting report templates.
2. Data Owner
• Monitoring and managing access information for business files in their compass.
3. Compliance Manager
• Configuring data, rules, and policy objects.
• Viewing data forensics.
• Monitoring and running most reports.
This part doesn't have the Report Template Administrator right.
4.Administrator
• View the admin dashboard and statistics.
• Monitoring and manager access information for all business files.
• Configure settings for DAS.
• Access rights granted to anyone with director capability.
• Report Templates Administrator right.
Connect to Identity Security Cloud
User situations in Identity Security Cloud define authorization sets assigned by administrators. Only ISC Admins can grant or remove them. Users may have multiple situations, combining all associated warrants.
Steps
1. Subscribe into your association (ISC).
2. Navigate to Admin > Identities > Identity List
3. For any being identity elect the perpendicular menu button.
4. Select the Set User Level option.
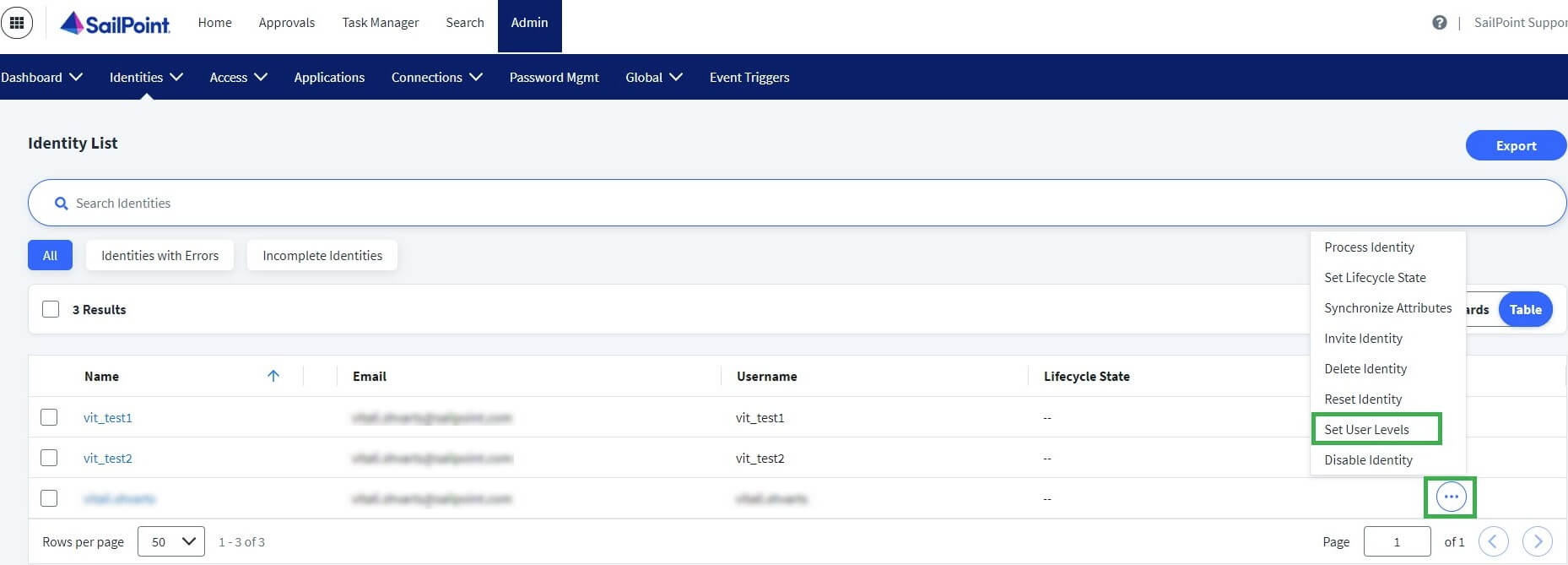
Scroll down and select the applicable Data Access Security parts
Select Save.
Data Access Security Virtual Appliance Cluster Creation
Data Access Security uses virtual appliances to connect to on- demesne or pall operations and sources. Specialized virtual appliances are also needed to perform Data Bracket across all operation types.
Application Infrastructure | Crawl | Permission Collection | Data Classification | Activity Monitoring |
|---|---|---|---|---|
Cloud (O365, AWS S3, etc.) | N/A | N/A | Data Access Security - Data Classification Collector | N/A |
On Premise (Windows Server, Netapp, etc.) | Data Access Security - Resource Collector | Data Access Security - Permission Collector | Data Access Security - Data Classification Collector | Data Access Security – Activity Monitor |
Connectors
O365 train Storage Microsoft OneDrive for Business
Microsoft SharePoint Online (Office 365)
Microsoft Exchange Online (Office 365)
Pall train Storage Box
Dropbox
Google Drive
NetApp
Powerscale
Unity SMB
Conclusion
SailPoint Data Access Security helps identify and protect sensitive unstructured data. It connects data access with user identities through Identity Security Cloud. Virtual Appliances enable discovery, permissions, classification, and monitoring. Overall, DAS reduces data risk and improves security and compliance.