Separation of Duties in SailPoint Identity Security Cloud
Date Posted:
Category:
Security
Author:
Sneha

Separation of Duties in SailPoint Identity Security Cloud
Date Posted:
Category:
Security
Author:
Sneha

Separation of Duties in SailPoint Identity Security Cloud
Date Posted:
Category:
Security
Author:
Sneha
Separation of Duties in Identity Security Cloud
Access is provided in any organization so that employees can complete their tasks quickly and efficiently. However, employees' access frequently increases as they transition between positions or take on new duties. This may eventually result in circumstances where users have permissions that inadvertently overlap and pose a risk.
This problem is made more structured by SailPoint Identity Security Cloud's Separation of Duties (SoD). It makes it easier to strike a balance between essential security controls and daily productivity by enabling organizations to identify these overlaps early and make sure that responsibilities are distributed appropriately. In actuality, access isn't always taken away when someone switches roles. Access may follow people as they change teams, take on temporary duties, or assist with other functions. People may eventually have more control over corporate procedures than was initially planned as a result.
Although this might not be immediately apparent, it can lead to situations where one individual can independently perform several delicate tasks, which is something that most organizations try to avoid. By continuously assessing access across identities and highlighting instances of conflicting permissions, ISC assists in identifying these hidden risks. SoD policies offer continuous visibility into possible conflicts as access changes, rather than depending solely on recurring reviews or audits to identify problems. ISC improves governance without interfering with people's daily tasks by clearly defining which access combinations should not coexist. It gives companies the assurance they need to keep things under control while still enabling workers to do their jobs well.
What SoD Does Inside ISC?
Fundamentally, SoD in ISC assists companies:
Identify conflicting access
Track your exposure to risk.
Continue to exercise internal control.
ISC helps teams identify areas of risk in their environment by regularly assessing identity access and pointing out infractions of internal policies. Instead of depending solely on audits, ISC enables companies to:
Monitor infractions
Create reports
Implement corrective measures
This provides a clear picture of who has risky access combinations for both the governance and operational teams.
The Practical Operation of SoD:
Every SoD policy includes:
Two lists of access
A violation occurs if a user has access to both lists.
For instance:
- Create a Vendor Approve Payment Access List A Access List B
- ISC recognizes a conflict when an identity possesses both.
- This illustrates the idea that people shouldn't have complete control over sensitive processes, like recording and issuing financial transactions.
Configuring SoD in ISC Tenant:
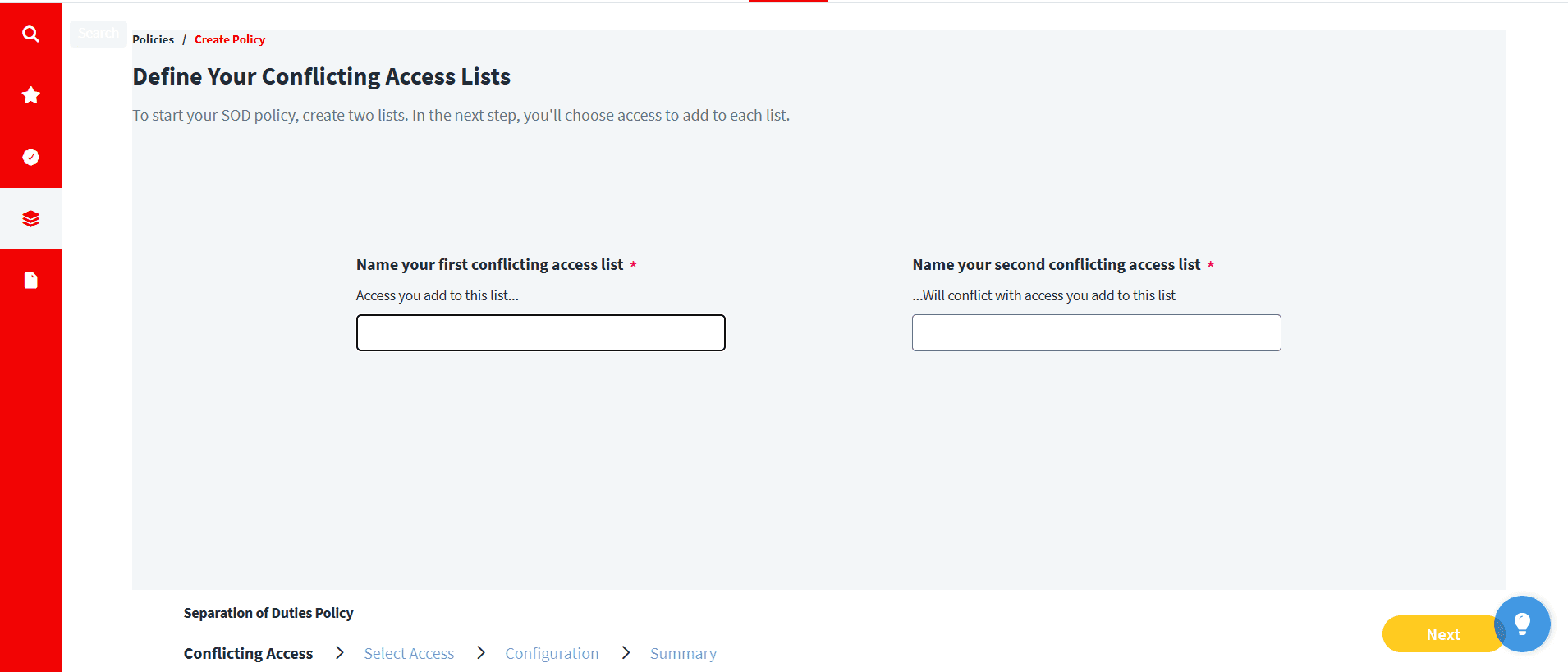
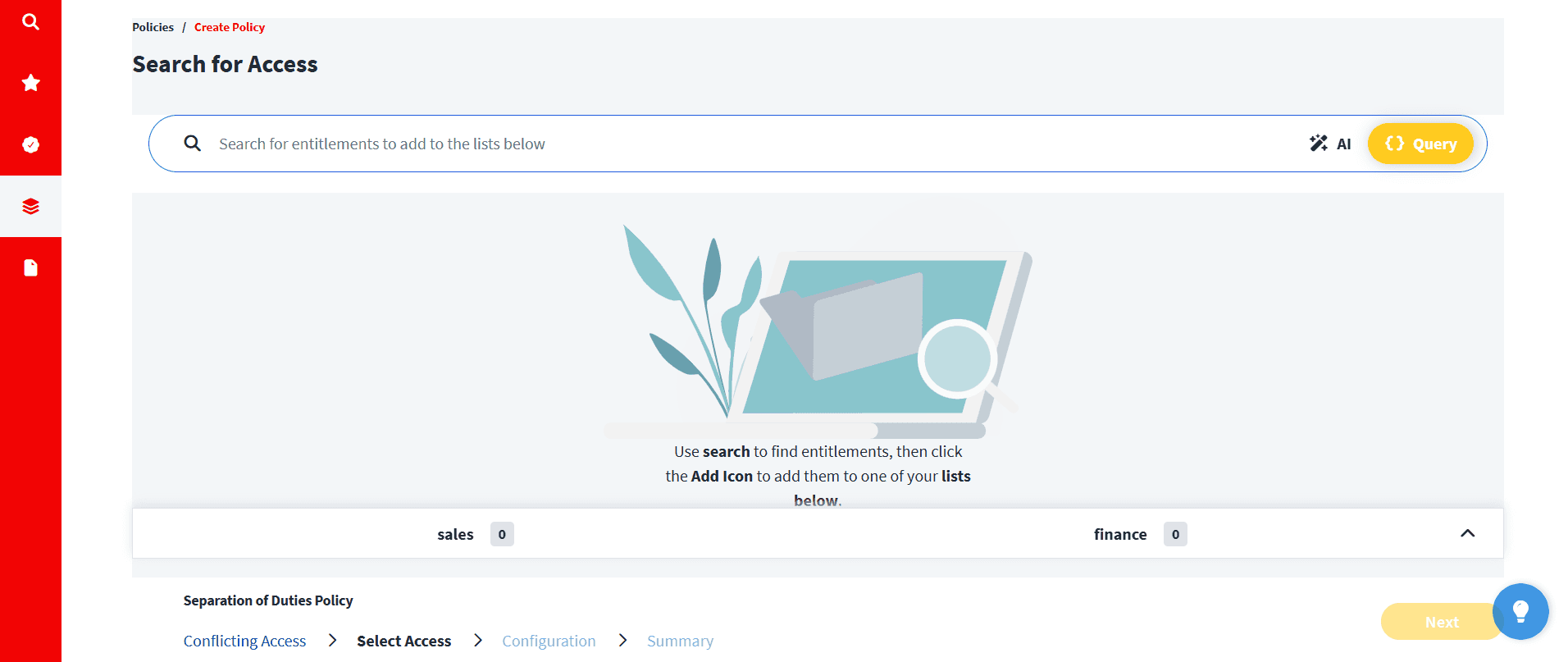
The below shows the initial step of creating a Separation of Duties (SoD) policy in ISC, here which defines conflicting access combinations. In this case, administrators make two distinct access lists to reflect duties that shouldn't be given to the same person. Just you need to name the lists here.
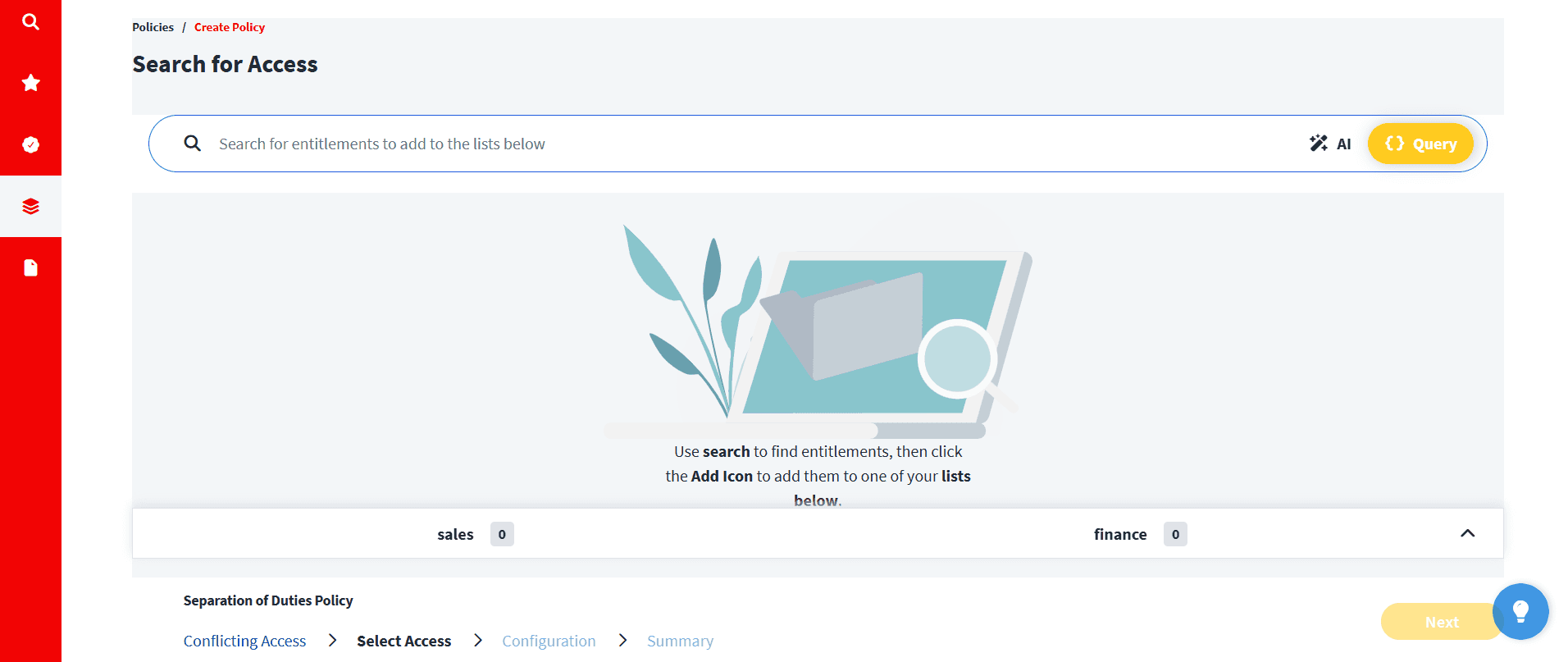
Here Administrators can assign particular permissions to each list, like Sales or Finance, by using search query and choosing them from connected applications. By including these entitlements in the lists, ISC is able to determine which access combinations should be regarded as conflicting and to reflect the actual access that users have in systems. After configuration, ISC detects a possible SoD violation if any user has entitlements from both lists.
After this we need to configure policy details like,
Policy name
Description
Policy and violation owners
External references
Risk tags
This helps link technical controls with business context.
Turn on the monitoring
ISC starts automatically assessing identities once it is enabled. It keeps an eye on current access, recently granted access, Reports highlight violations, enabling teams to act swiftly.
Additionally, organizations can get alerts about infractions; download reports; and monitor the status of remediation. Then they can also do
Subscribe to violation notifications
Download reports
Track remediation progress
In ISC, separation of duties (SoD) is a continuous governance process that is backed by constant reporting, monitoring, and policy updates. Up to 500 SoD policies can be maintained by organizations, providing coverage in crucial domains like operations, IT, and finance. When properly configured, SoD ensures that access stays in line with internal control expectations without interfering with daily operations. It also helps limit excessive access, protect sensitive business processes, enhance governance visibility, and support audit readiness.
Conclusion:
To sum up, ISC's Separation of Duties is essential for assisting organizations in effectively and methodically managing access risk. Better control over crucial tasks is made possible by ISC, which detects conflicting permissions and continuously monitors user access. It guarantees that no one person has undue influence over important business procedures. Organizations can identify possible risks early and take appropriate action with well-defined policies. A robust security posture is sustained over time by ongoing governance through reporting and monitoring. By coordinating access with internal control standards, it also promotes audit readiness. Additionally, it enables workers to carry out their jobs effectively and without needless interruption. This offers the visibility required to preserve the harmony between security and productivity as access environments continue to change. It lowers operational risk and improves governance when properly applied. In the end, SoD in ISC assists organizations in creating a framework for access that is more secure and accountable.
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Category:
Security
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Category:
Category:
Security
Security
Get your
Tailored Quote for your
Organisation
Get your
Tailored Quote for your
Organisation
Separation of Duties in Identity Security Cloud
Access is provided in any organization so that employees can complete their tasks quickly and efficiently. However, employees' access frequently increases as they transition between positions or take on new duties. This may eventually result in circumstances where users have permissions that inadvertently overlap and pose a risk.
This problem is made more structured by SailPoint Identity Security Cloud's Separation of Duties (SoD). It makes it easier to strike a balance between essential security controls and daily productivity by enabling organizations to identify these overlaps early and make sure that responsibilities are distributed appropriately. In actuality, access isn't always taken away when someone switches roles. Access may follow people as they change teams, take on temporary duties, or assist with other functions. People may eventually have more control over corporate procedures than was initially planned as a result.
Although this might not be immediately apparent, it can lead to situations where one individual can independently perform several delicate tasks, which is something that most organizations try to avoid. By continuously assessing access across identities and highlighting instances of conflicting permissions, ISC assists in identifying these hidden risks. SoD policies offer continuous visibility into possible conflicts as access changes, rather than depending solely on recurring reviews or audits to identify problems. ISC improves governance without interfering with people's daily tasks by clearly defining which access combinations should not coexist. It gives companies the assurance they need to keep things under control while still enabling workers to do their jobs well.
What SoD Does Inside ISC?
Fundamentally, SoD in ISC assists companies:
Identify conflicting access
Track your exposure to risk.
Continue to exercise internal control.
ISC helps teams identify areas of risk in their environment by regularly assessing identity access and pointing out infractions of internal policies. Instead of depending solely on audits, ISC enables companies to:
Monitor infractions
Create reports
Implement corrective measures
This provides a clear picture of who has risky access combinations for both the governance and operational teams.
The Practical Operation of SoD:
Every SoD policy includes:
Two lists of access
A violation occurs if a user has access to both lists.
For instance:
- Create a Vendor Approve Payment Access List A Access List B
- ISC recognizes a conflict when an identity possesses both.
- This illustrates the idea that people shouldn't have complete control over sensitive processes, like recording and issuing financial transactions.
Configuring SoD in ISC Tenant:
The below shows the initial step of creating a Separation of Duties (SoD) policy in ISC, here which defines conflicting access combinations. In this case, administrators make two distinct access lists to reflect duties that shouldn't be given to the same person. Just you need to name the lists here.
Here Administrators can assign particular permissions to each list, like Sales or Finance, by using search query and choosing them from connected applications. By including these entitlements in the lists, ISC is able to determine which access combinations should be regarded as conflicting and to reflect the actual access that users have in systems. After configuration, ISC detects a possible SoD violation if any user has entitlements from both lists.
After this we need to configure policy details like,
Policy name
Description
Policy and violation owners
External references
Risk tags
This helps link technical controls with business context.
Turn on the monitoring
ISC starts automatically assessing identities once it is enabled. It keeps an eye on current access, recently granted access, Reports highlight violations, enabling teams to act swiftly.
Additionally, organizations can get alerts about infractions; download reports; and monitor the status of remediation. Then they can also do
Subscribe to violation notifications
Download reports
Track remediation progress
In ISC, separation of duties (SoD) is a continuous governance process that is backed by constant reporting, monitoring, and policy updates. Up to 500 SoD policies can be maintained by organizations, providing coverage in crucial domains like operations, IT, and finance. When properly configured, SoD ensures that access stays in line with internal control expectations without interfering with daily operations. It also helps limit excessive access, protect sensitive business processes, enhance governance visibility, and support audit readiness.
Conclusion:
To sum up, ISC's Separation of Duties is essential for assisting organizations in effectively and methodically managing access risk. Better control over crucial tasks is made possible by ISC, which detects conflicting permissions and continuously monitors user access. It guarantees that no one person has undue influence over important business procedures. Organizations can identify possible risks early and take appropriate action with well-defined policies. A robust security posture is sustained over time by ongoing governance through reporting and monitoring. By coordinating access with internal control standards, it also promotes audit readiness. Additionally, it enables workers to carry out their jobs effectively and without needless interruption. This offers the visibility required to preserve the harmony between security and productivity as access environments continue to change. It lowers operational risk and improves governance when properly applied. In the end, SoD in ISC assists organizations in creating a framework for access that is more secure and accountable.