ServiceNow & SailPoint ISC Integration: Access Management
Date Posted:
Category:
Security
Author:
Gopi

ServiceNow & SailPoint ISC Integration: Access Management
Date Posted:
Category:
Security
Author:
Gopi

ServiceNow & SailPoint ISC Integration: Access Management
Date Posted:
Category:
Security
Author:
Gopi
ServiceNow Service Catalog & Service Desk Integration with SailPoint Identity Security Cloud (ISC)
Most identity programs don't crash because the tools aren't good enough. They crash because access requests, approvals, oversight, and delivery are spread across different systems that were never meant to talk to each other.
Here's the reality in most companies: your employees live in ServiceNow. Their managers live in ServiceNow. The people who own critical applications? Also in ServiceNow, day in and day out. That's where actual work happens—where people ask for things, where approvals get signed off, where the business keeps running.
But the rules about who should have access? Those live over in SailPoint Identity Security Cloud. The access models, the segregation-of-duties rules, the compliance evidence that auditors will eventually come asking for—that's SailPoint's world.
When these two worlds don't connect, everything falls apart. Approvals happen outside any governance framework. Provisioning turns into a manual mess with no consistency. And when audit time rolls around? You're stuck playing a painful game of "let's piece together what happened" across systems that don't line up.
ServiceNow and SailPoint Identity Security Cloud tackle this problem from different perspectives, and when you connect them properly, they create one unified, smooth access management experience.
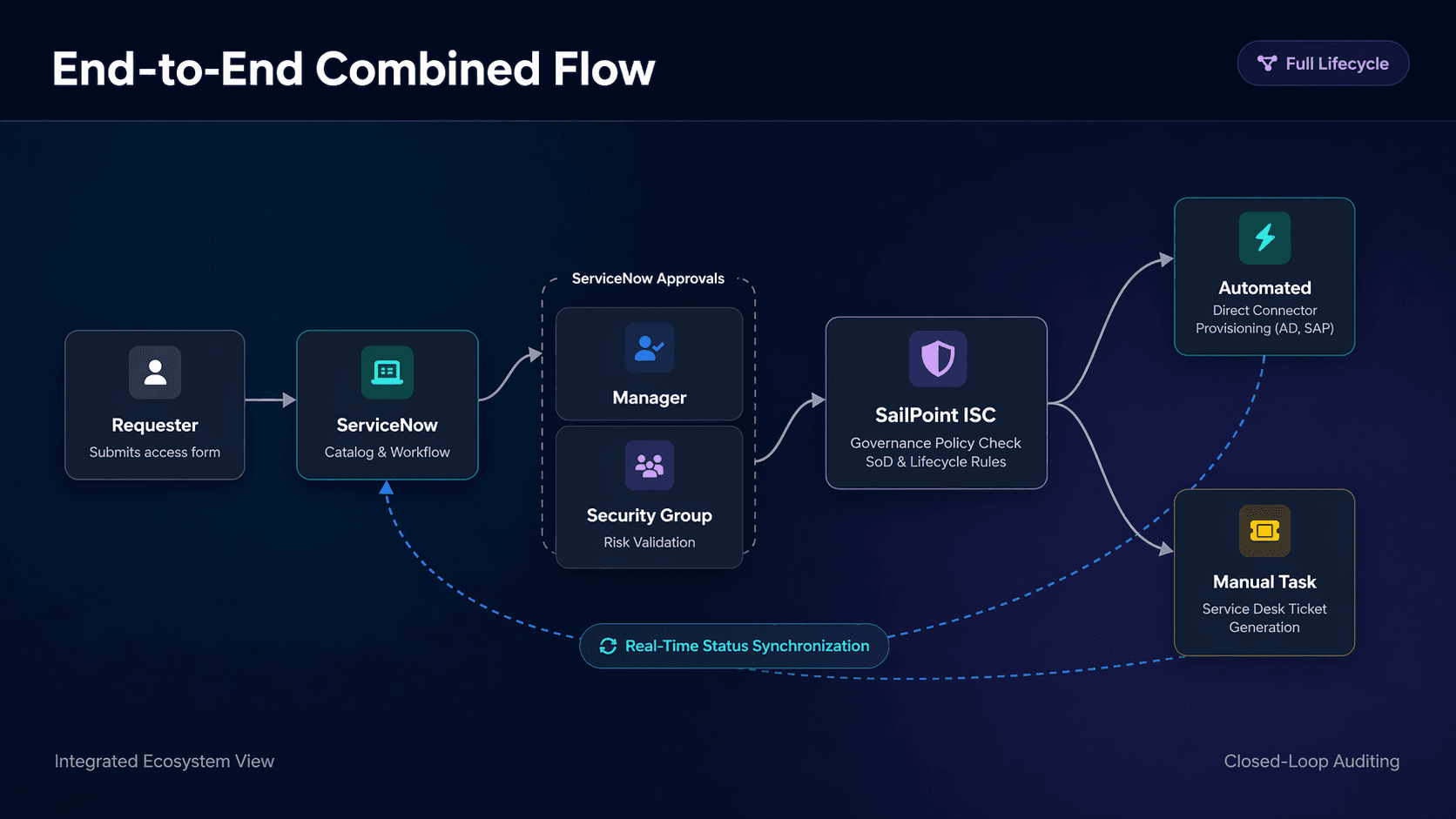
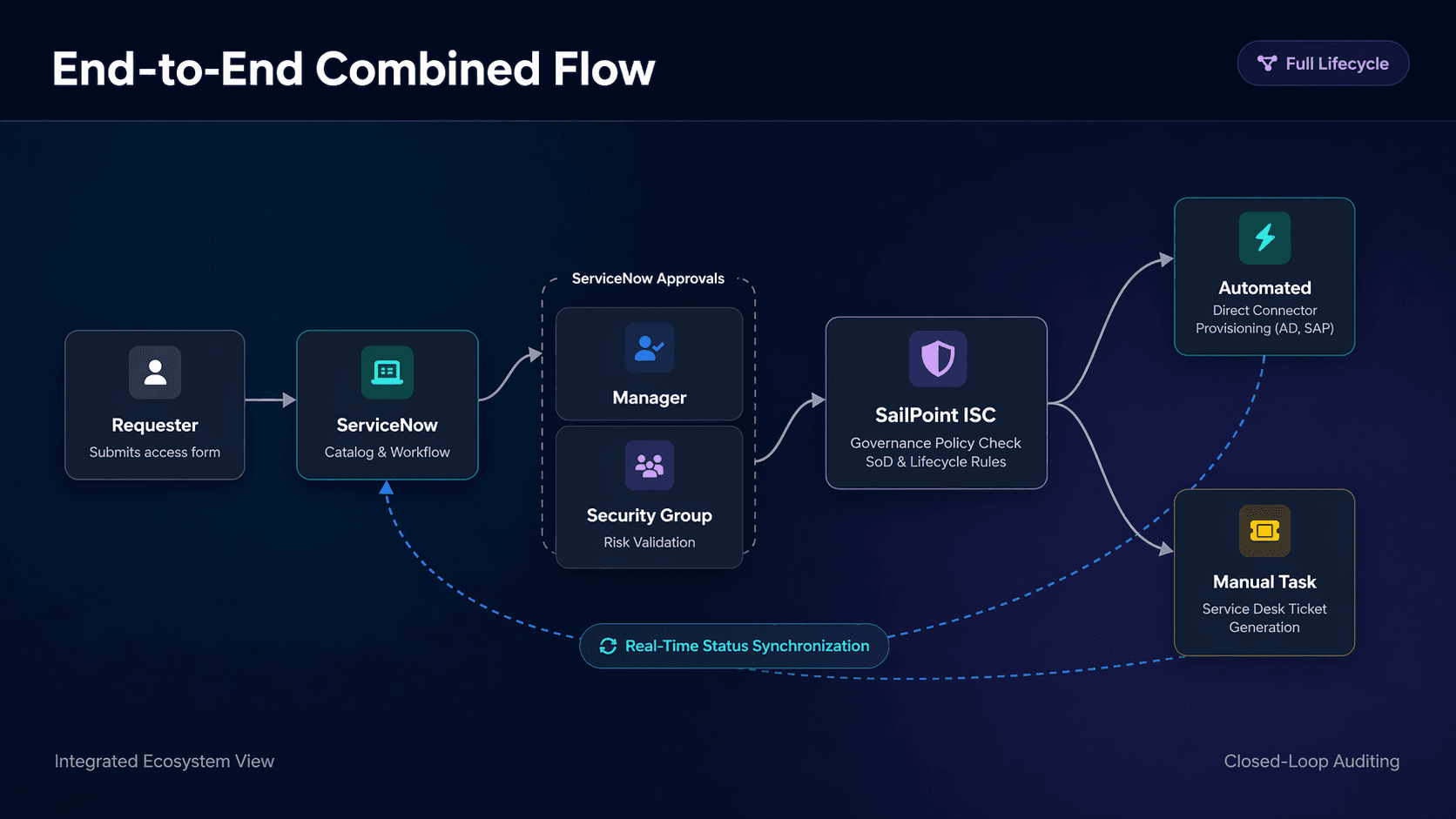
The integration brings these worlds together without stepping on anyone's toes. ServiceNow stays the friendly face that everyone already knows and uses. It handles the human side—the requests, the conversations, the approvals. SailPoint ISC stays in the background as the quiet authority that actually decides whether access should be granted based on your policies and compliance rules.
Making Integration Part of How You Work
The setup is refreshingly straightforward. Someone requests access through the ServiceNow portal they already use every day. The request flows through ServiceNow's standard approval steps—usually starting with their manager, then maybe to application owners or security folks if needed. Nothing changes for them.
Once everyone's signed off, ServiceNow securely passes the request to SailPoint ISC using REST APIs and OAuth authentication. Simple, secure, and completely behind the scenes.
Now here's where the baton passes. SailPoint ISC becomes the source of truth. It checks everything against governance policies and determines whether the request should actually go through. The actual provisioning might happen automatically or it might need some hands-on work through the ServiceNow's Service Desk module. Either way, updates flow back to ServiceNow throughout the process, so users and managers can always know what's happening with their request no black holes, no other guessing games.
This approach allows for the ServiceNow to manage the user experience and the workflow while SailPoint is enforcing the identity decisions and compliance standards. Each system does what it does best, and together they create something that actually works for everyone—employees, managers, IT, and auditors alike.
Foundation Before Integration
Implementations do not begin with the first API call. SailPoint ISC requires a clean access model. Applications have to be onboarded correctly, roles and entitlements defined clearly, segregation-of-duties policies defined in terms of the business risk that they mitigate. Identity lifecycle states need to express how access is granted and removed over time.
On the ServiceNow side sits the official SailPoint Service Catalog app, ushering in a supported integration framework. Auth flows through OAuth, striding in secure and leaving an audit trail. There’s no db-level access, no custom shortcuts – everything winds its way through supported APIs.If the access model is weak, ServiceNow will not hide the problem—it will expose it faster.
ServiceNow as the Front Door
Once the ServiceNow application is installed, ServiceNow becomes the single entry point for access requests. Users interact with familiar catalog items rather than identity tools. They request access using simple forms that capture business justification and context without exposing technical complexity.
Behind the scenes, ServiceNow prepares a governance-ready request. The simplicity of the user experience is deliberate. Complexity belongs in the governance engine, not the portal.
Approvals That Align with Accountability
Approvals remain fully within ServiceNow. Managers validate business need. Application owners or security teams validate application-specific risk. Routing is dynamic, ensuring requests reach the correct approvers without manual intervention.
SailPoint ISC does not replicate or override these approvals. Instead, it consumes the approved request and applies governance rules that approvals alone cannot enforce.
Governance Begins in SailPoint ISC
Once the request reaches SailPoint ISC, it is evaluated against policy. Role eligibility, entitlement constraints, segregation-of-duties conflicts, lifecycle state, and risk policies are all applied consistently. Even a fully approved request can be rejected at this stage if it violates governance rules.
This separation is critical. Approval confirms intent. Governance confirms permissibility.
Provisioning Without Compromising Control
For applications with connectors, SailPoint ISC provisions access automatically and reliably. For systems that cannot be integrated directly, SailPoint triggers ServiceNow Service Desk tasks. The service desk fulfills access manually, but SailPoint remains in control of the request lifecycle, waiting for confirmation before closing the access event.
Manual work is allowed, but manual decisions are not.
Visibility, Audit, and Trust
Throughout the lifecycle, status updates flow back to ServiceNow. Users see progress in real time. Managers see outcomes without chasing tickets. Auditors see a single, traceable story—from request to approval to policy decision to fulfillment.
Nothing is reconstructed after the fact. Evidence is created as part of the process.
What This Integration Ultimately Delivers
When implemented correctly, the ServiceNow and SailPoint ISC integration becomes more than a connector. It becomes an operating model for access governance. Users get a familiar experience. Security teams get consistent policy enforcement. IT teams reduce manual work. Auditors get clarity instead of explanations.
That is why this integration has become the enterprise standard for organizations that take identity seriously.
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Category:
Security
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Stay tuned to our blog to see more posts about
Sailpoint products implementation and its related updates.
Category:
Category:
Security
Security
Get your
Tailored Quote for your
Organisation
Get your
Tailored Quote for your
Organisation
ServiceNow Service Catalog & Service Desk Integration with SailPoint Identity Security Cloud (ISC)
Most identity programs don't crash because the tools aren't good enough. They crash because access requests, approvals, oversight, and delivery are spread across different systems that were never meant to talk to each other.
Here's the reality in most companies: your employees live in ServiceNow. Their managers live in ServiceNow. The people who own critical applications? Also in ServiceNow, day in and day out. That's where actual work happens—where people ask for things, where approvals get signed off, where the business keeps running.
But the rules about who should have access? Those live over in SailPoint Identity Security Cloud. The access models, the segregation-of-duties rules, the compliance evidence that auditors will eventually come asking for—that's SailPoint's world.
When these two worlds don't connect, everything falls apart. Approvals happen outside any governance framework. Provisioning turns into a manual mess with no consistency. And when audit time rolls around? You're stuck playing a painful game of "let's piece together what happened" across systems that don't line up.
ServiceNow and SailPoint Identity Security Cloud tackle this problem from different perspectives, and when you connect them properly, they create one unified, smooth access management experience.
The integration brings these worlds together without stepping on anyone's toes. ServiceNow stays the friendly face that everyone already knows and uses. It handles the human side—the requests, the conversations, the approvals. SailPoint ISC stays in the background as the quiet authority that actually decides whether access should be granted based on your policies and compliance rules.
Making Integration Part of How You Work
The setup is refreshingly straightforward. Someone requests access through the ServiceNow portal they already use every day. The request flows through ServiceNow's standard approval steps—usually starting with their manager, then maybe to application owners or security folks if needed. Nothing changes for them.
Once everyone's signed off, ServiceNow securely passes the request to SailPoint ISC using REST APIs and OAuth authentication. Simple, secure, and completely behind the scenes.
Now here's where the baton passes. SailPoint ISC becomes the source of truth. It checks everything against governance policies and determines whether the request should actually go through. The actual provisioning might happen automatically or it might need some hands-on work through the ServiceNow's Service Desk module. Either way, updates flow back to ServiceNow throughout the process, so users and managers can always know what's happening with their request no black holes, no other guessing games.
This approach allows for the ServiceNow to manage the user experience and the workflow while SailPoint is enforcing the identity decisions and compliance standards. Each system does what it does best, and together they create something that actually works for everyone—employees, managers, IT, and auditors alike.
Foundation Before Integration
Implementations do not begin with the first API call. SailPoint ISC requires a clean access model. Applications have to be onboarded correctly, roles and entitlements defined clearly, segregation-of-duties policies defined in terms of the business risk that they mitigate. Identity lifecycle states need to express how access is granted and removed over time.
On the ServiceNow side sits the official SailPoint Service Catalog app, ushering in a supported integration framework. Auth flows through OAuth, striding in secure and leaving an audit trail. There’s no db-level access, no custom shortcuts – everything winds its way through supported APIs.If the access model is weak, ServiceNow will not hide the problem—it will expose it faster.
ServiceNow as the Front Door
Once the ServiceNow application is installed, ServiceNow becomes the single entry point for access requests. Users interact with familiar catalog items rather than identity tools. They request access using simple forms that capture business justification and context without exposing technical complexity.
Behind the scenes, ServiceNow prepares a governance-ready request. The simplicity of the user experience is deliberate. Complexity belongs in the governance engine, not the portal.
Approvals That Align with Accountability
Approvals remain fully within ServiceNow. Managers validate business need. Application owners or security teams validate application-specific risk. Routing is dynamic, ensuring requests reach the correct approvers without manual intervention.
SailPoint ISC does not replicate or override these approvals. Instead, it consumes the approved request and applies governance rules that approvals alone cannot enforce.
Governance Begins in SailPoint ISC
Once the request reaches SailPoint ISC, it is evaluated against policy. Role eligibility, entitlement constraints, segregation-of-duties conflicts, lifecycle state, and risk policies are all applied consistently. Even a fully approved request can be rejected at this stage if it violates governance rules.
This separation is critical. Approval confirms intent. Governance confirms permissibility.
Provisioning Without Compromising Control
For applications with connectors, SailPoint ISC provisions access automatically and reliably. For systems that cannot be integrated directly, SailPoint triggers ServiceNow Service Desk tasks. The service desk fulfills access manually, but SailPoint remains in control of the request lifecycle, waiting for confirmation before closing the access event.
Manual work is allowed, but manual decisions are not.
Visibility, Audit, and Trust
Throughout the lifecycle, status updates flow back to ServiceNow. Users see progress in real time. Managers see outcomes without chasing tickets. Auditors see a single, traceable story—from request to approval to policy decision to fulfillment.
Nothing is reconstructed after the fact. Evidence is created as part of the process.
What This Integration Ultimately Delivers
When implemented correctly, the ServiceNow and SailPoint ISC integration becomes more than a connector. It becomes an operating model for access governance. Users get a familiar experience. Security teams get consistent policy enforcement. IT teams reduce manual work. Auditors get clarity instead of explanations.
That is why this integration has become the enterprise standard for organizations that take identity seriously.